The future of MIM as we see it
What is the future of MIM? Is Microsoft Identity Manager reaching end of life? Do I need to move to another platform? What are the options? Here’s our take.
Background | MIM alternatives | Why implement MIM now | FAQs | Microsoft-friendly tools to augment and/or replace MIM | Conclusion
Who is this blog for?
People often ask us if it’s the end of the road for MIM and what they should do next. I aim to present some answers in this blog.
From the original release of Microsoft Identity Integration Server almost 20 years ago to the current rich, ever-expanding, modern feature set of Microsoft Entra ID, the Microsoft identity stack continues to be an incredible success. This blog assumes that you are already on your journey towards the modern, cloud-oriented world that Microsoft Entra ID/Microsoft Office can provide, but that MIM is still an important part of your infrastructure. Like many of our customers, you may also be wondering what to do next as MIM’s “end of life” approaches in 2029.
The blog goes into some detail about the MIM functionality which can’t (as yet) be migrated to the cloud. It provides some guidance, from the perspective of a long-term Microsoft partner, about various courses of action you might take. It discusses some Microsoft-friendly tools that can augment, partially replace, or fully replace MIM.
If you are looking for a blog about the huge benefits of Microsoft Entra ID, or a general discussion of all the vendor platforms available for managing your cloud identities, this is not the blog you are looking for. But, if you’re looking for our opinion about what is the future of MIM, read on!
Also, see these answers to some recent questions on MIM upgrade and deployment from Mark Wahl, Microsoft’s IAM/IGA software architect, and Principal Program Manager.
Background
The MIM Legacy
In the Microsoft world, MIM (or its predecessors) has been the mainstay of identity management for almost two decades. It has proved to be affordable, flexible, and robust, and has been deployed successfully in all sorts of environments. Much of its functionality can be (and is being) smoothly migrated to the cloud (to Microsoft Entra ID (formerly Azure AD)), but there are some functions that Microsoft Entra ID does not cover, and which MIM covers very well. Some customers are not ready to migrate any functionality to Microsoft Entra ID.
MIM is now in extended support and will be so until early 2029. If you have a Microsoft Entra ID Premium subscription you still get standard support with a few caveats. After that various paid-for support options will be available from Microsoft or partners like Oxford Computer Group. And in any case, your MIM solution will not suddenly stop working. Meanwhile, Microsoft continues to release functionality in its cloud offerings that can replace MIM functionality (though as yet that is not a total replacement).
What comes after MIM?
Microsoft is well aware of the varied identity and access management requirements that exist, and they are developing their Microsoft Entra ID capabilities to cover these, so the answer to this question will need to be reevaluated over time. At the time of writing (as discussed above) there are more than 4 years available to either:
- Replace MIM entirely with Microsoft Cloud functionality (Microsoft Entra ID)
- Replace most of the MIM functionality with Microsoft Cloud functionality, and select and implement a product (presumably from a Microsoft-friendly vendor) to replace the remaining functionality
- Stay with MIM because the level of support needed can be provided by (for example) OCG, along, perhaps, with enhancements provided by additional products
- Migrate to a different vendor altogether
Should we move to another platform?
This is plenty of time, and there is no need to rush into an implementation that may not turn out to be optimal – we can’t be sure right now what things will look like in 2029. It is the case that many organizations are doing new implementations of MIM (particularly MIM sync) because it represents a relatively cheap and effective solution even if (as a worst case) it only lasts for 4 years. These organizations are not short-sighted, they are pragmatic.
If an organization is minded to move to another vendor anyway, then perhaps there is no reason to hold back – but switching to another vendor just to replace certain MIM functionality is a risk, and should certainly not be rushed into. Identity and Access Management (IAM) is changing, and any vendor offering may become obsolete. At Oxford Computer Group (OCG) – sadly – we have come across some very expensive, very time-consuming migrations to other vendor platforms, which in some cases do not even work properly. We have even achieved considerable annual savings for customers migrating to MIM from other vendor platforms.
We also see script-based solutions being sold as IAM. While these can be quick and cheap to install, they lack the robustness and integrity that an IAM solution demands. This kind of approach can end up polluting Active Directory with poor-quality data, which compromises later phases of IAM (such as role management and privileged access management).
It is worth noting that anyone with Microsoft Entra ID Premium can use MIM free of charge, so migrating away from it could be (at best) an expensive way of only getting to where you are now. If your processes are well sorted out and embedded in MIM, the right kind of controlled migration may be quite easy, while replacing the entire platform may be like going back to square one.
Having taken soundings from Microsoft, other partners, and our customers, we are confident that Microsoft will replace MIM functionality with technologies that offer a tight fit to Microsoft Entra ID, and that meet changing IAM requirements.
Why implement MIM now?
On the Microsoft platform, MIM is still the only game in town when it comes to integrating Active Directory with sources of truth such as HR (with a few exceptions). License fees are very much at the modest end of the range, while the cost of implementation is comparable to other proper IAM systems.
It offers just about everything you need now, and, at the time of writing, for at least 6 years. There are paths available, or opening up, to support the move to hybrid cloud, and perhaps one day to cloud-only – or simply away from MIM if that turns out to be the right choice.
Ask us about your situation!
Of course, every customer has a unique situation, and the best course of action is not the same for everyone. While Oxford Computer Group is a very strong Microsoft partner, our expertise and experience are wide – we do not rely on software sales for our income, and we aim for an impartial view of the best way forward. In addition, we have developed several extensions and/or replacements for certain Microsoft IAM components, which provide additional options for the future. We are all about enabling the cloud, but we recognize that this is not the whole story. So please talk to us before doing anything you might regret! The following FAQs may help.
Frequently Asked Questions
Can MIM SSPR be migrated to Microsoft Entra ID?
Yes. Microsoft Entra ID Premium includes self-service password reset (SSPR) in the cloud. If Microsoft Entra Connect’s password writeback feature is in use, a user can reset their on-premises AD password (as well as their Microsoft Entra ID cloud password via password hash synchronization). Although not an exact feature for feature replacement, Microsoft Entra ID Premium SSPR can easily be argued to be more convenient, and more secure, than that available through the MIM Portal.
Can MIM group management be migrated to Microsoft Entra ID?
Mostly. Azure Premium provides broadly the same functionality for cloud groups, as the MIM Portal does for on-premises groups. However, at the time of writing, while on-premises groups can be synchronized up to the cloud, write-back from cloud groups to on-premises groups is limited to distribution lists – you can’t write back to on-premises security groups (at least in supported configurations). It would not be surprising if this changed soon, but if the management of on-premises security groups is a must right now, then some additional tools will be required if the MIM Portal is to be replaced (see below).
Can MIM provisioning be migrated to Microsoft Entra ID?
Some now, more later, maybe everything eventually. MIM is highly flexible when it comes to provisioning, but it generally requires code to be written. MIM can also be extended to connect to just about any system by writing more code in the form of an “ECMA2” (effectively a custom connector).
Microsoft Entra ID provides excellent functionality for the codeless provisioning of accounts into many cloud-based systems. It can also provision to on-premises applications using SCIM, or to legacy applications using the very same ECMA2 “connectors” that MIM uses. This latter capability is an invitation-only preview at the time of writing, but it is clear enough where this is going. So, although there are a few caveats, and this is not a feature for feature replacement, it does look as though Microsoft Entra ID will have this area pretty well covered.
Can Microsoft Entra ID handle multiple sources of truth (like HR systems) like MIM?
Not yet. The MIM synchronization engine is particularly good at connecting to, and importing identity data from, multiple sources of truth (HR, temporary staff, student enrolment, etc.), and then generating an authoritative, canonical representation of each identity. Microsoft Entra ID (along with Microsoft Entra Connect) has limited capability in this regard. So, in all but the simplest situations, this remains one area where a MIM, or a 3rd party tool, is still required (see below). However, a lot can – and probably will – happen in the next 4 years.
Is there a migration path for PCNS?
Not at present as far as we know. The Password Change Notification Service (PCNS) captures AD password changes and forwards them to MIM, which can send them to target systems. If you use PCNS we recommend that you stick with MIM for the time being. We know of at least one vendor who plans to provide an alternative – so watch this space.
Can MIM Portal workflows be replaced by Microsoft Entra ID functionality?
Not directly. In our experience, many organizations are using some fairly simple workflows (for example for group management approvals), which can be readily replaced by comparable functionality in Microsoft Entra ID. However, a small but important percentage of organizations have invested significantly in MIM workflows and/or other MIM portal functionality – for such cases there is no obvious Microsoft migration path. This has prompted OCG to make investments in cloud functionality (within Azure) which can provide a migration path (see below).
How can we replace BHOLD functionality?
BHOLD was a role management addition to the MIM synchronization engine; it is now effectively deprecated. The role management within Microsoft Entra ID is much more sophisticated in its approach, and may well be all that is needed for an organization intending to be cloud-oriented. However, Microsoft Entra ID does not offer generic on-premises role management, so any organization looking for an equivalent to MIM plus BHOLD functionality will likely have to look for a 3rd party tool (see below).
Microsoft-friendly tools to augment and/or replace MIM
There are many tools available that can add functionality to MIM, support migration away from MIM, or even replace MIM altogether. We present just three here. The criteria for selection are:
- No pressure to move away from the Microsoft platform (this is what we mean by “Microsoft friendly”)
- Fully supportive of MIM (can co-exist), with a clear migration path to something else (can replace)
- We have experience implementing them, so can give you authoritative information
In the interests of full disclosure, we have to say that two of these tools are from Oxford Computer Group companies.
 The Identity Panel Suite from SoftwareIDM
The Identity Panel Suite from SoftwareIDM
This suite is cloud-based, is centered around and complementary to, Microsoft Entra ID, and is comprised of 5 applications:
- Identity Panel itself: can import data from cloud and on-premises sources, providing auditing, monitoring (health), reporting, and workflow features (triggered by changes to identity data, or based on date/time) – the key message here is that it can do all this for MIM, including scheduling it
- HyperSync Panel: a general-purpose synchronization engine for on-premises and cloud systems, including cloud to cloud – the key message here is that it is a replacement for the MIM synchronization engine (with improvements)
- Access Panel: a generic role management application, including RBAC, ABAC, SoD, attestation campaigns, etc. – the key message here is that it is a replacement for BHOLD (and much more)
- Service Panel: is a web-based and fully customizable portal for managing identity data – white pages for users, a user-management tool for managers, and a service desk (for administrators and help-desk) – the key message here is that this is a more or less complete replacement for the MIM Portal
- Test Panel: a generic, automated testing application for your identity management system – this is entirely additional to MIM functionality.
In summary, the Identity Suite can be put in place alongside MIM, AD, and Microsoft Entra ID – adding capabilities to the platform, then it can facilitate a gradual migration from MIM, replacing those features that Microsoft Entra ID can’t. SoftwareIDM see themselves as much more than a replacement for MIM (with justification), but for our purposes here, they represent a total replacement for MIM.
We have run a series of five webinars to show how you can enhance your Microsoft-based identity management solution and prepare for the future with SoftwareIDM’s Identity Panel Suite. You can view the webinar recordings here. Each one includes an overview and a demo.
IBIS from Trusted-ID
Trusted-ID (www.trusted-id.eu) is an Oxford Computer Group company based in The Netherlands. That country has some very particular expectations from an Identity Management platform, driven by government requirements. Over the years, Trusted-ID has extended the capabilities of MIM to meet those requirements. The resulting product has an impressive feature list, including:
- Can be used in addition to MIM or instead of MIM
- Extensive logging and reporting
- Can be deployed on-premises only, off-premises (Azure) only, or in hybrid (combined) environments
- Event-driven (while MIM is state-driven)
- Optimized for Azure (monthly Azure costs approximately $300-$400)
- Subscription basis
- Regular pen-testing and updates (with security patches if required after pen-testing)
- Imminent releases:
- Multitenancy
- Smartphone app for approvals (assets, authorizations, onboarding, etc.)
- Over 100 standard reports, and growing
This diagram is in Dutch, but gives an impression of the breadth and depth of Trusted-IDs investment in their customers’ needs (this is a subset of features).
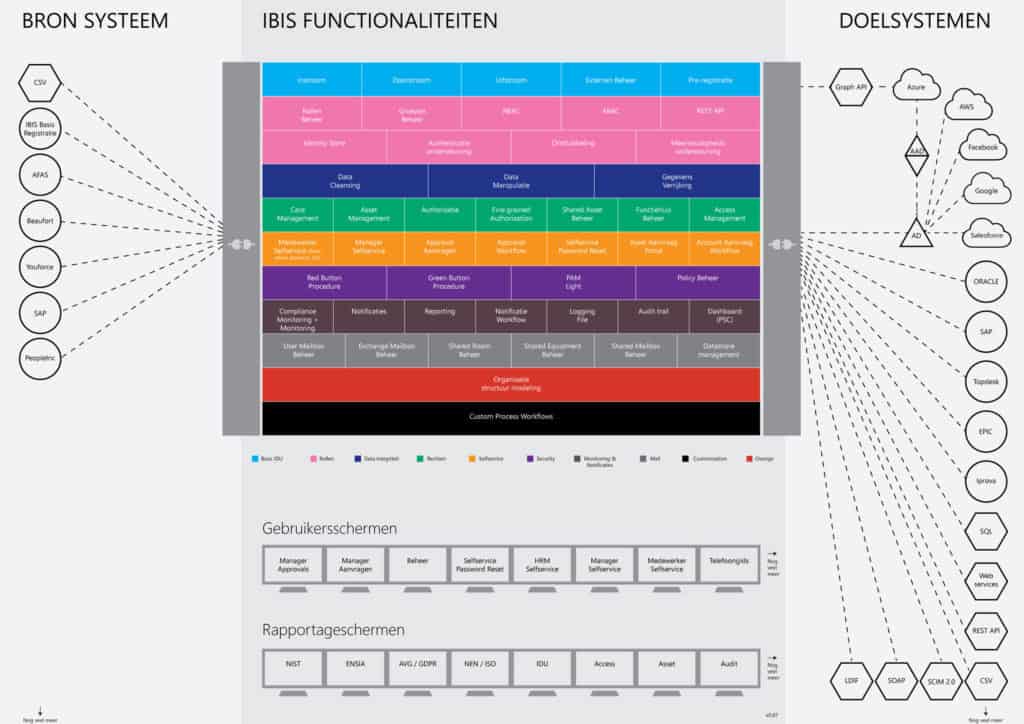
Of course, this may not apply to every organization, but it goes to how deep and wide our knowledge is in this area, and hopefully, you can see how seriously we take the business of supporting our customers. For more information, please visit the Trusted-ID website.
IDABUS
Oxford Computer Group Germany (OCG DE), has produced some excellent extensions to the MIM Portal over many years, including a better interface, role management, and reporting. IDABUS, from OCG DE’s subsidiary of the same name, is a cloud-based solution that does everything that the MIM Portal can do and much more (except things done better by Microsoft Entra ID, such as SSPR).
It is completely Azure-based (no local servers needed), and uses a subscription model. (An on-premises version is planned for high-security environments or customers with no Cloud connections.)
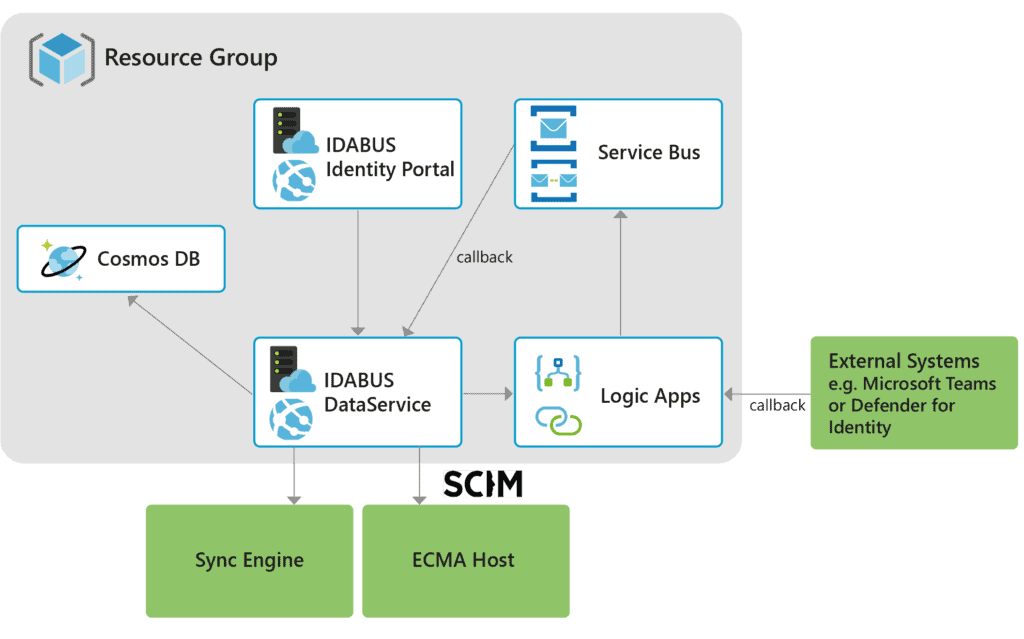 The feature set is that of the MIM Portal, plus
The feature set is that of the MIM Portal, plus
- Roles-Based Access Control
- Reporting with restore capabilities on each object
- Very fast resource history, with restore options
- Event Graph, which is a representation of all data events related to any object in the system – a powerful tool for troubleshooting and auditing
- Preview/simulation/cancel/correct/resume features for workflows
- Workflows with complex scenarios (sophisticated approval flows)
- Time-triggered workflows
- Connection to any Rest API
- Extended XPATH language with a visual builder
- Extensible schema (users, groups, roles, cost centers, org structures, etc.)
- Configuration changes without downtime
- MIM migration Tool available (with security checks)
In summary, this is the MIM Portal on steroids!
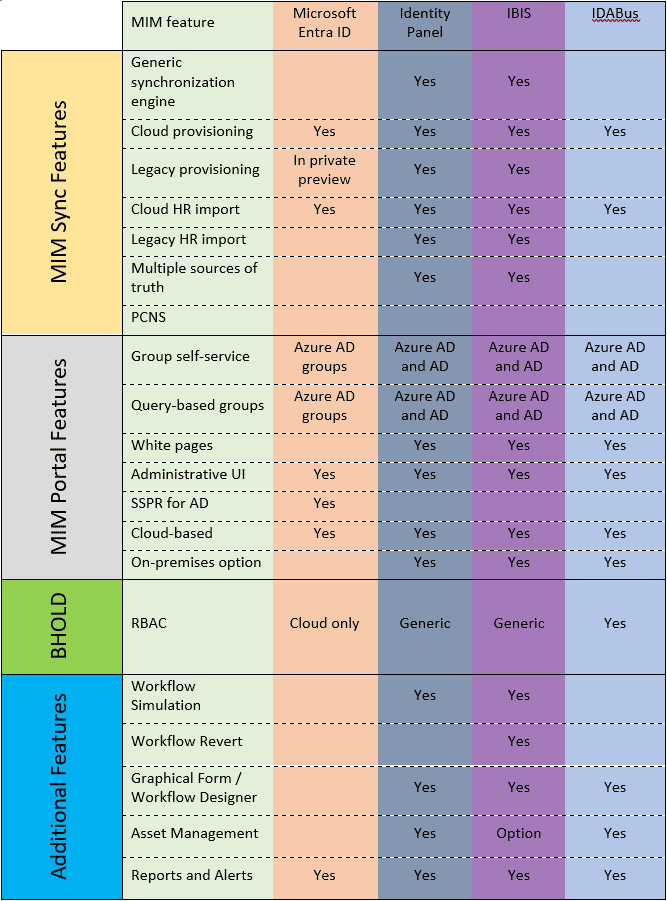
Quick reference
This table shows which features are native to which systems:
Conclusion
Don’t panic! We have at least 6 years to track Microsoft’s developments and put in place alternatives as required. There is already some choice for how to replace MIM functionality, and the next 6 years will bring more choice. If you feel you need to move now, then talk to us – we can help you make good choices.
Talk to us!
Oxford Computer Group has been a very strong Microsoft partner for over 30 years, with wide expertise and experience.
- We do not rely on software sales for our income. We try to present an impartial view of the best way forward.
- We have developed several extensions and/or replacements for certain Microsoft identity and access management components which provide additional options for the future.
- We offer industry-leading training courses covering all you need to know to implement and support your Microsoft IAM and get the most out of your cloud investment.
Please contact me if you have any questions or if you would like to know more!
Need training?
Our industry-leading MIM training courses are available at three levels: Foundation, Advanced, and Expert. We offer:
- Live instructor-led training via Teams from wherever you are
- Online at your own pace – start any time
- Private training exclusively for your IT team – learning together is a top team-building exercise
MIM Foundation MIM Advanced MIM Expert